Organizations Must Be Ready to Assess Potential Security Risks to Protect Everyone
Frank Costa, President Nexgen Protection Services –
Security leaders across environments — spanning retail stores, corporate businesses, residential communities and cities — should prepare for threats that will require fast and informed action. We all have experienced major cultural moments, including the 2020 election, COVID-19 pandemic, and nationwide protests.
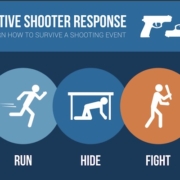
It is critical for organizations to put in place security protocols to preserve employee and public safety while respecting the rights of citizens. Creating a plan and protocols to address these incidents will help you ensure a coordinated response.
- Establish communication protocols. Create clear communication protocols that explain how information will flow to key parties, such as store or business leadership, employees, customers, neighboring businesses and law enforcement.
- Assess physical defense measures. How can you protect your building from damage or control the flow of traffic and people?
- Promote de-escalation tactics. Reinforce your communication protocols during this training. Ensure that the safety of every employee and customer is the number one priority, reminding them to not get involved if physical violence occurs.
- Implement safety technology. Cameras, alarms, motion detectors, and motion-triggered lights can all bring visibility to situations, add necessary deterrence if you make the decision to close a location, and gather evidence to help law enforcement pursue bad actors. Revisit your existing security investments to assess their capabilities, and consider whether you need new solutions to cover your gaps.
SOURCE:
Kelley, M. 3 potential security risks to stay ahead of post-election, Security Magazine, 11/20/2024.
#protectionservices #securitystandards #publicsaftey #mobilesecurity #securitythreats